Android devices have a special lock screen with a 3 x 3 grid of dots. Users can set an "unlock pattern" by connecting the dots in a specific sequence, forming a series of joined line segments where each segment's endpoints are two consecutive dots in the sequence. A sequence of k dots is a valid unlock pattern if both of the following are true:
2 and 9 without dots 5 or 6 appearing beforehand is valid because the line from dot 2 to dot 9 does not pass through the center of either dot 5 or 6.1 and 3 without dot 2 appearing beforehand is invalid because the line from dot 1 to dot 3 passes through the center of dot 2.Here are some example valid and invalid unlock patterns:
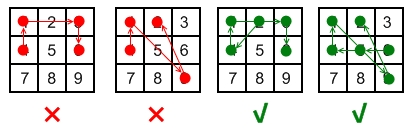
[4,1,3,6] is invalid because the line connecting dots 1 and 3 pass through dot 2, but dot 2 did not previously appear in the sequence.[4,1,9,2] is invalid because the line connecting dots 1 and 9 pass through dot 5, but dot 5 did not previously appear in the sequence.[2,4,1,3,6] is valid because it follows the conditions. The line connecting dots 1 and 3 meets the condition because dot 2 previously appeared in the sequence.[6,5,4,1,9,2] is valid because it follows the conditions. The line connecting dots 1 and 9 meets the condition because dot 5 previously appeared in the sequence.Given two integers m and n, return the number of unique and valid unlock patterns of the Android grid lock screen that consist of at least m keys and at most n keys.
Two unlock patterns are considered unique if there is a dot in one sequence that is not in the other, or the order of the dots is different.
Example 1:
Input: m = 1, n = 1 Output: 9
Example 2:
Input: m = 1, n = 2 Output: 65
Constraints:
1 <= m, n <= 9Problem Overview: Count how many valid unlock patterns can be formed on the Android 3x3 lock screen using lengths between m and n. A pattern cannot revisit a key, and moves that jump over another key are only allowed if that intermediate key has already been used.
Approach 1: Brute Force Backtracking (O(9!))
The straightforward strategy generates every possible path on the 3×3 grid using depth‑first search. Start from each digit (1–9), mark it visited, and recursively try the remaining digits while respecting the Android rule: if a move crosses another key (for example 1 → 3 crossing 2), that intermediate key must already be visited. A small lookup table called skip stores these required intermediate nodes. The search continues until the path length reaches n, counting patterns whose length is at least m. Time complexity is O(9!) in the worst case because permutations of keys are explored, and space complexity is O(9) for the recursion stack and visited array.
Approach 2: Symmetry Optimized Backtracking (O(9!))
The grid has strong symmetry. Corners (1,3,7,9) behave the same, edges (2,4,6,8) behave the same, and the center (5) is unique. Instead of running DFS from all nine digits, run it once from a representative of each group and multiply the result. For example, compute patterns starting from 1 and multiply by four for the corners. Do the same for 2 multiplied by four for edges, and handle 5 once. The same skip matrix enforces the rule about crossing intermediate keys. This reduces redundant exploration while keeping the same theoretical complexity O(9!), with space O(9). This approach is what most production solutions use because it cuts the constant factor dramatically.
Approach 3: Bitmask + DP State Exploration (O(9 * 2^9))
A more algorithmic perspective models the problem as state transitions. Each state is defined by the current key and a bitmask representing visited keys. From a state (node, mask), iterate over all possible next digits and check whether the move is valid using the same intermediate-key rule. Memoizing results for identical states avoids recomputation. The number of states is bounded by 9 * 2^9, giving time complexity around O(9 * 2^9) and space complexity O(9 * 2^9). This version connects naturally to dynamic programming and bitmask techniques.
Recommended for interviews: Symmetry‑optimized backtracking is the expected solution. It demonstrates control of DFS, constraint handling, and pruning using problem structure. Interviewers like seeing the skip matrix plus the symmetry observation because it reduces work from nine starting searches to three. Mentioning the bitmask state idea also shows familiarity with backtracking and DP tradeoffs.
Python
Java
C++
Go
TypeScript
| Approach | Time | Space | When to Use |
|---|---|---|---|
| Brute Force Backtracking | O(9!) | O(9) | Understanding the full search space and Android movement rules |
| Symmetry Optimized Backtracking | O(9!) | O(9) | Best practical solution; reduces repeated DFS using grid symmetry |
| Bitmask Dynamic Programming | O(9 * 2^9) | O(9 * 2^9) | When modeling states formally or demonstrating DP with bitmasking |
LeetCode 351. Android Unlock Patterns • Happy Coding • 6,342 views views
Watch 8 more video solutions →Practice Android Unlock Patterns with our built-in code editor and test cases.
Practice on FleetCode